Article
Supply chain attacks: Understanding one of cybersecurity’s biggest threats
If you’re part of the cybersecurity world, you probably heard about XZ Utils Backdoor—a maliciously crafted backdoor that was implanted into an open-source data-compression utility that merged into all major Linux distributions. Without a patch, the XZ Utils Backdoor would have allowed attackers to perform Remote Code Execution on infected systems. This attempt represents one of the best executed supply chain attacks thus far, but despite the seriousness of the situation, news of the XZ Utils backdoor didn’t really spread beyond the cybersecurity world. This is, in part, due to the lack of understanding outside of the cybersecurity community.
Cyber criminals are continuously pushing the envelope of possibility when it comes to attacking the internet, and, like this attack, they are getting more and more sophisticated in their endeavors. As such, it’s more important than ever for people outside of the cybersecurity community to have a better understanding of this type of attack and the techniques we can use to mitigate it—everyone has a role to play in cybersecurity.
[I]t’s more important than ever for people outside of the cybersecurity community to have a better understanding of this type of attack and the techniques we can use to mitigate it.
What does it all mean?
First, let’s break down and define some of the terms I used in my description of the XZ Utils backdoor.
Supply Chain Attack – A type of cyberattack where attackers indirectly attempt to infiltrate an organization or system through vulnerabilities of its upstream supplier or provider in order to compromise the integrity of the final product or service.
Backdoor – Code that allows an attacker to discreetly access your system whenever they want.
Open-Source – Applications or programs where all of the source code is publicly available, allowing anyone to contribute to the project.
Utility – A small application that performs a specific function that can be used by other programs and protocols of a computing system. For instance, XZ Utils is a data compression utility that increases the efficiency of storing and sending data from computers.
Remote Code Execution – When an attacker is allowed to run code and commands on an infected system like they were logged into it and sitting in front of the system.
Linux Distributions – Linux is an open-source Operating System that is an alternative to Microsoft Windows. Being open-source, many companies have made their own customizations on top of the Linux foundation, which they package and sell. The biggest distributions of Linux include Red Hat and Debian. While distributions are different “flavors” of Linux, they utilize many of the same Linux-based utilities.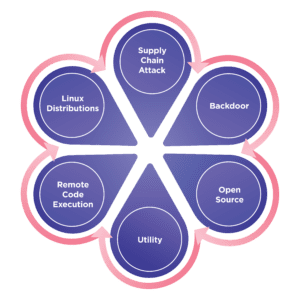 Putting it all together
Putting it all together
XZ Utils is an open-source project that is publicly accessible on a popular website for creating and sharing programming code called GitHub. In 2021 the bad actors created a GitHub account. In early 2022, they contributed code to XZ Utils project on GitHub for the first time. This early contribution did not include malicious code and was intended to make the user account appear legitimate. The backdoor code was introduced in 2023 and if it had not been caught, it would have been included in system updates to millions of systems worldwide and allowed these bad actors to access every system where the code was used. Fortunately, the code was discovered in time and a patch was released to remove the code and prevent it from being used.
How can you protect yourself?
This was an extremely advanced, long-term operation carried out by skilled attackers and represents the dangers of open-source software and supply chain attacks to organizations. Even though this type of attack is complex, the preventative measures are relatively simple.
First, it’s vital to properly vet your IT vendors. With supply chain attacks you have no control over what your vendors do to protect themselves or the software code they use, which can create a scary dependency. Knowing your IT partner is trustworthy and secure is key.
Second, practicing good cyber hygiene is imperative. You can do this by completing security updates as soon as they’re available on all of your applications. As the security industry uncovers attacks like this, security updates are released that patch the vulnerabilities discovered.
Finally, reconsider your use of open-source code and be extremely cognizant of where open-source code is used in your environment. Being publicly available, anyone has the access to examine and suggest changes to open-source code. This access means these code repositories are prime suspects for attackers like the ones behind the XZ Utils backdoor.
At Altera, we have security teams working 24/7 to stay on top of the latest security trends and ensure the safety of our products and environments. To learn more about Altera’s cybersecurity efforts, check out some of my previous blogs here and here.

